When Zero-Days Are Cheap, Attack Surface Is A Liability
I loved being a guest on today’s Cyber Risk Alliance webinar with Adrian and wanted to share some of my additional notes and thoughts in case you missed the live show (or prefer reading my weekly newsletter).
The Mythos and Daybreak hype cycle’s missing the whole point. Niels Provos proved it with his IronCurtain framework: swap in Sonnet 4.6 for $30 a run, or Opus 4.6 for $150, and you get about the same zero-days Anthropic gated behind Project Glasswing at $25/$125 per million tokens. Vidoc Security replicated 80%+ of the public Mythos findings using GPT-5.4 and Opus 4.6 inside an open-source agent. The moat isn’t the model. It’s the scaffolding, and that’s replicable if you’re willing to have your team spend some time prompting the model. If I were running a team for the DPRK or China’s MSS, it’s what people’s bonuses and performance reviews would be tied to.
Meanwhile, James Kettle’s about to open-source the HTTP Terminator at Hacker Summer Camp, a system that doesn’t just find bugs but invents new attack classes. When the person who popularized HTTP Request Smuggling gives away a tool that autonomously discovers novel desync triggers, the “too dangerous to release” argument sounds like the marketing claim that it is.
So what should the blue team do? The answer isn’t “wait for a patch,” because those are going to get de-compiled and analyzed at speed. We already have Copy Fail (CVE-2026-31431), a 732 byte exploit that works deterministically on every Linux distribution (and were the coordinated vulnerability disclosure doesn’t seem to have been great). CISA says it’s already being exploited in the wild. Sean Heelan’s January 2026 experiments showed GPT-5.2 generating 40+ distinct exploits for a single zero-day in under an hour. If your defense plan is “deploy the patch when it ships,” you’re betting against time you no longer have.
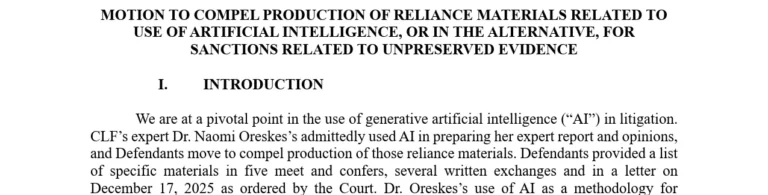
The ongoing Marquis v. SonicWall litigation should make every general counsel and CISO nervous. Marquis had MFA enabled, a patched firewall, and standard controls – all the right things, all more than a year before LLMs turned out to be fancy exploit generators. And they still got hit with ransomware, because SonicWall’s cloud backup API leaked unencrypted MFA scratch codes. SonicWall initially claimed 5% of customers were affected, then revised that number upwards to 100%. Now Marquis is suing SonicWall upstream, and that case is going to be rewriting how courts think about liability in supply chain attacks.
If your compliance documentation shows you treated zero-days as someone else’s problem, that’s going to be a problem for your legal team. Attack surface management isn’t optional anymore, and neither is microsegmentation or any of the other things that didn’t really go far enough when CISO’s tried to talk about Zero Trust to the Board, instead of talking about business risks. If it’s internet-exposed, assume it’s going to see an exploit before the patch arrives. Plan accordingly, or plan to explain yourself to a judge.